This a simple, straight-to-the-point guide on what DoD Contractors need to do to comply with NIST 800-171 quickly and effectively so that they can continue provide services to the Department of Defense. While this guide was written to be simple for company executives and management to understand, the requirements and language of 800-171 absolutely require either an experienced IT department or an outside consultant, such as a Managed Security Service Provider (MSSP) who specializes in DoD compliance.
A detailed guide specifically written for IT professionals is out of the scope of this guide. Fortunately, the National Institute of Standards and Technology (NIST) has already made available the documentation necessary for an experienced IT department to follow.
With that said, here’s what DoD Contractors need to do to comply with NIST 800-171…
The Documents: SSP & POA&M
As we recently reported, the Department of Defense has released its final guidance with respect to how DoD Contractors are to address DFARS/NIST 800-171 cyber security requirements during the contract award process. The guidance specifies the delivery of two documents by the DoD contractor:
- Security Systems Plan (SSP) and;
- Plan-of-Action and Milestones (POA&M)
These two documents serve as the basis for providing evidence of compliance with NIST 800-171 to the Department of Defense. While this is not an official requirement by the DoD, contractors who do not include these documents are at a severe disadvantage against contractors who are. Subcontractors who deal directly with Prime contractors may also find themselves required to provide proof of compliance to the Prime.
Security Systems Plan (SSP)
The Security Systems Plans goes over the DoD contractor’s approach for complying with the NIST 800-171 guidelines during the pre-contract phase and the security measures that they currently have in place. If the organization wants to continue doing business with the DoD, they need to ensure that the Security Systems Plans are up to par and formatted in a way that’s usable for the bidding process.
Options for Developing an SSP:
DoD Contractors have two options to develop a System Security Plan:
- NIST SSP Template: DoD Contractors who have an internal IT Department who has cyber security knowledge can opt to develop an SSP in-house. The DoD has a SSP template available to assist in the process. To download the SSP template, click here.
- Outsource to an MSSP: A Managed Security Service Provider who provides NIST 800-171 compliance services can develop the SSP for you for a fee. To view learn more about our compliance services for NIST 800-171, click here.
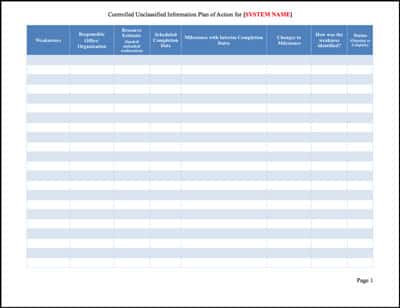
Plan-of-Action and Milestones (POA&M)
Compliance gaps identified during this process need a Plan-of-Action and Milestones on how the contractor intends on fixing the issues and what controls they’re putting in place that go beyond the minimum standard. The DoD uses NIST 800-171 as a baseline for the cybersecurity requirements that it wants to see from contractors working with CUI.
Options for Developing an POA&M:
DoD Contractors have two options to develop a Plan-of-Action and Milestones:
- NIST POA&M Template: DoD Contractors who have an internal IT Department who has cyber security knowledge can opt to develop a POA&M in-house. NIST has a POA&M template available to assist in the process. To download the POA&M template, click here.
- Outsource to an MSSP: A Managed Security Service Provider who provides NIST 800-171 compliance services can develop the POA&M for you for a fee. To view learn more about our compliance services for NIST 800-171, click here.
NIST 800-171: At the Heart of the SSP & POA&M
At the heart of both documents is the framework developed by the National Institute of Standards and Technology (NIST), known as NIST SP 800-171. The framework was designed to provide guidance on the best practices for protecting Controlled Unclassified Information (CUI), which is the objective of Defense Acquisition Federal Regulation Supplement (DFARS). Your IT network configuration and the way you handle CUI will need to comply with this framework.
NIST 800-171 Requirements
There are 14 primary requirements in this publication that the DoD contractor needs to account for when assessing their compliance efforts. Agencies that fail to comply with these security controls can find themselves missing out on DoD contracts.
- Access Control: Only a limited set of users and devices should have access to CUI.
- Awareness and Training: Everyone working at DoD contractors should have a role-appropriate awareness of the common cyber threats that can lead to a data breach.
- Auditing and Accountability: The DoD contractor’s systems should be capable of leaving a digital paper trail.
- Configuration Management: The wrong configuration can lead to many vulnerabilities, so a security-centric option is necessary.
- Identification and Authentication: The contractor’s systems need a way to confirm that users are who they claim to be.
- Incident Response: The DoD contractor should be prepared for common situations that could lead to the CUI being at risk of a breach.
- Maintenance: The DoD contractor’s information systems and infrastructure require proactive maintenance to remain up-to-date.
- Media Protection: Any media that stores CUI needs sufficient protection to protect it from breaches, along with procedures in place to wipe the media before destroying it.
- Personnel Security: The DoD contractors need to screen employees who are working with CUI and ensure that login information is not valid after someone leaves the organization.
- Physical Protection: Physical protection is required for the servers and hard drives that contain CUI.
- Risk Assessment: Regularly scheduled risk assessments keep the DoD contractor on top of any new risks to CUI.
- Security Assessment: Security audits are another important compliance measure in this publication.
- System and Communications Protection: The DoD contractor’s information systems need IT security measures that control all access of information and actively monitor for a potential intrusion.
- System and Information Integrity: The organization’s information systems should have sufficient defenses against malware, bugs and other vulnerabilities.
- IT Department: DoD Contractors who have an internal IT Department with cyber security knowledge and experience may be able to understand and implement the network environment and security protocols necessary to meet 800-171 security controls.
- Outsource to an MSSP: A Managed Security Service Provider who provides NIST 800-171 compliance services will have an experienced team equipped with the tools and processes to help contractors meet the security controls. To view learn more about our compliance services for NIST 800-171, click here.
To view the complete documentation, please see “Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations” document provided by NIST.
Options for Meeting the Requirements
DoD Contractors have two options to meet the requirements:
Technical Assistance is Available
We hope this guide gets you closer toward achieving NIST 800-171 compliance. If you have any questions about which options work best for your company, please feel free to give us a call at (866) 583-6946. We’ve helped DoD Contractors and IT departments all over the U.S. navigate the complexities of NIST 800-171. We’re more than happy to jump on the phone and point you in the right direction.